LAS VEGAS—You install surveillance cameras to protect the security and privacy of your home or business. If someone commits a break-in, you have a video record. But what if you’re not the only one watching those cameras? What if the camera is vulnerable to hacking? You may not be the only one who can tap into the camera’s feed, and at the Black Hat security conference, security researchers revealed exactly how easy it can be.
Noam Moshe, vulnerability researcher with cyber-physical security firm Claroty and member of Claroty’s Team82, did a deep dive into cameras made by Axis Communications, a Swedish company and a major producer of security cameras and related hardware. Axis operates above the consumer level, supplying security for governments, schools, hospitals, and Fortune 500 companies (aka, you won’t find it in our roundup of consumer-oriented home security cameras).
Moshe found some serious problems, which he presented to attendees. But don’t run to throw a towel over your cameras. Axis has patched the flaws in its software, so as long as you get the update, you should be fine. As for the next hack (and there will be a next hack), we can only hope it’s found by Moshe and his team, not by hackers with bad intentions.
Easy Remote Camera Control Means Others Get Easy Access, Too
“My day job is to look for vulnerabilities on all sorts of devices, and responsibly disclose them,” said Moshe. “It’s my playground.” This particular project began when he scanned the internet for unsecured ports and discovered some of them using an unfamiliar service called axis.remoting. “When I see a service that’s esoteric, that’s my cue,” Moshe explained.
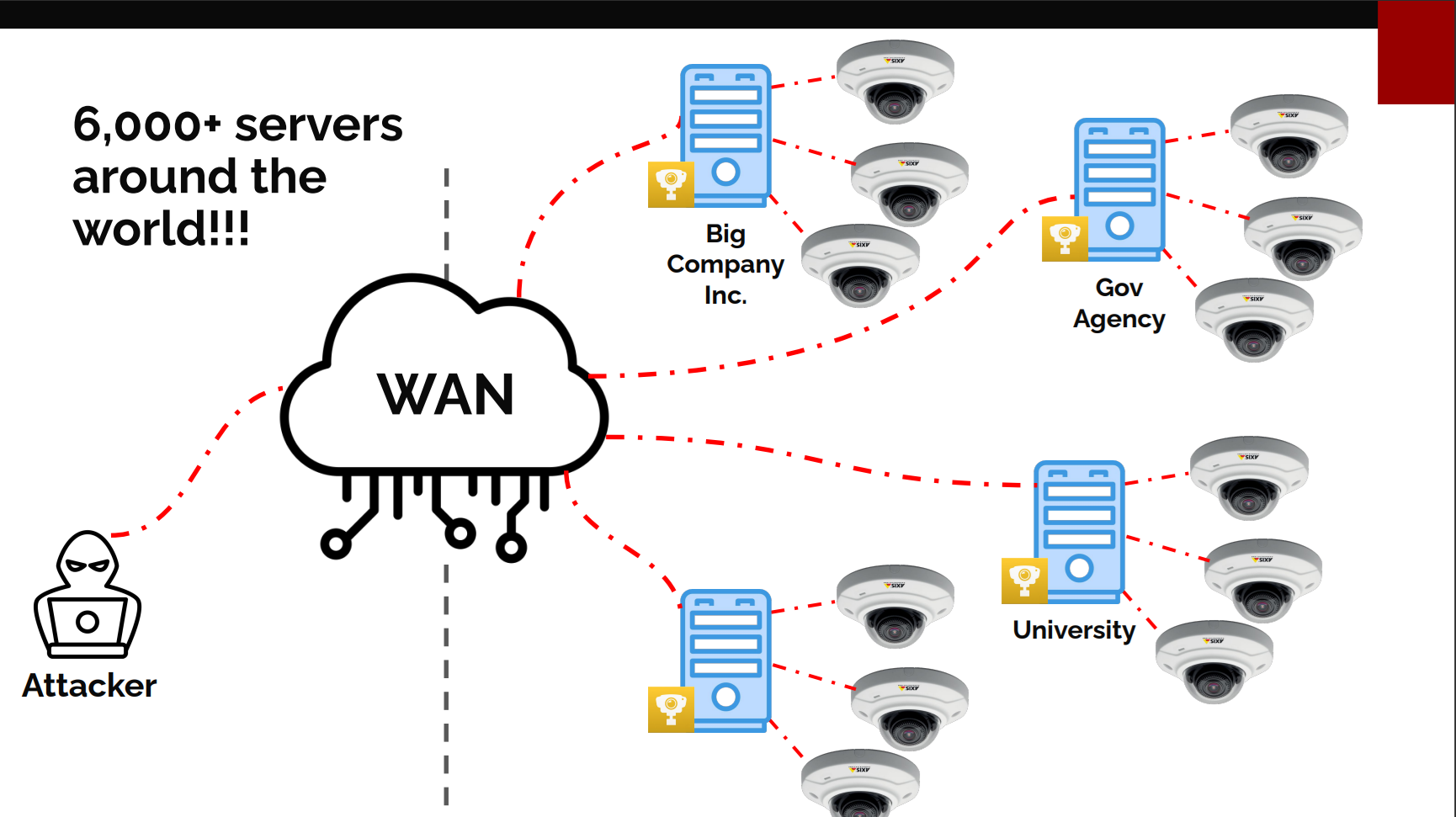
He said that Axis is a major security camera vendor for large companies with hundreds of cameras in multiple locations. Remote access is a must, and Axis offers two versions, one that’s extremely secure and expensive, and one that’s less expensive but exposes the axis.remoting service he discovered. Naturally, the latter is more popular.
Moshe explained that the Axis software grants its own device manager complete control over your fleet of cameras, and that can lead to problems (and unintentional access to other people’s cameras, too). “Then Axis Camera Station comes into play. From one central location, you can consume all the live feeds,” he explained. The team focused on hacking these server-side apps, their client apps, and, of course, the cameras.

As with many Black Hat presentations, Moshe’s success came from working through endless mistakes and blind alleys. Eventually, he parlayed his access to the point of taking full control of all the security cameras, which are basically tiny Linux computers.
With that degree of control in place, he extended the hack to the servers running Axis Device Manager and Axis Camera Station. “We can now execute code on the client, the server, and all the cameras,” he exulted. Remote execution of arbitrary code, essentially making a device do whatever you want because you can access it completely, is the holy grail of hacking, so this was a huge success.
Who Is Vulnerable?
“Moshe inquired, ‘Who is susceptible to this kind of assault?'” He then used thedevice-level search engine Shodanlooking for servers using the axis.remoting protocol. “I found 65,000 servers, with 4,000 located in the US,” he stated. “But who is operating these servers?” He demonstrated that a basic search revealed the server’s name, allowing him to determine the company.
We now have the capability to run code not only on the client and server, but also on every camera.
David Moshe, Claroty
“Why are there so many of them around?” he went on. “The market is becoming increasingly restricted. Numerous Chinese firms face prohibitions in both the United States and Europe.” Since Axis Communications is located in Sweden, it appears to be safe.
Moshe brought up the concept of responsible disclosure at the beginning of his presentation. He noted that when he shared his discoveries with Axis, the company reacted within a mere 10 minutes and immediately began working on a fix. “Axis’s response was likely among the quickest I’ve ever experienced,” Moshe stated. “However, it’s crucial that we ensure these security updates are implemented.”
This is the best possible outcome—researchers find a security flaw and notify the company, and a security patch quickly appears. But Moshe and his team keep seeking new flaws, as do teams of hackers. We can only hope the white hat teams reach the goal first. It’s even more reason to pay attention to good cybersecurity hygiene, whether you’re a big company or an at-home user.